Millions of consumers will soon be shopping for holiday gifts from their phones, tablets, laptops, and from work PCs. Retailers won’t be the only ones trying to get your hard-earned money. Cybercriminals typically come out aggressively during the holiday season to steal credit card numbers, identities, and online bank accounts.
One of the biggest cyber threats consumers are likely to face comes from man-in-the-middle attacks (MiTM). MiTM attacks make it possible for hackers to potentially see or manipulate Internet traffic that the user believes to be private. Almost any type of Internet connection can be hacked in this way if the end-user is compromised or the platform itself is vulnerable. MiTM attacks allow hackers to insert themselves between the user and the website or service they are trying to use. This allows them to read the victim’s emails, see what websites they’re visiting, steal valuable personal information, or impersonate the user by stealing session cookies, passwords, and more.
Keep in mind that MiTM attacks are nothing new. However, in recent years, criminals have found several ways to reinvent this classic attack. To make matters worse, a variety of inexpensive tools, such as the WiFi pineapple, are readily available online that make it easy for almost anyone to conduct these attacks.
Here are six ways you could get hacked by a man-in-the-middle attack this holiday season…
1. WiFi Eavesdropping

Image Source:https://wifitraining.com/
One of the oldest and most common forms of man-in-the-middle is the WiFi attack. It involves hijacking a WiFi connection in order to spy on the user. This attack is more likely to happen in a public WiFi connection, such as a coffee shop, airport, or hotel, but it can also happen in the privacy of your own home. Hackers have several ways to hijack a WiFi connection. First, they can create a fake WiFi node (called an “evil twin”) that impersonates a legitimate WiFi access point in order to trick you into connecting to it. Another way is to “sniff” your web traffic over an unencrypted connection and look for things like session cookies to hijack your accounts. Or, an attacker could simply hack your WiFi password to get access.
2. Man-in-the-Browser
Image Source:https://stackoverflow.com/questions/
One of the world’s most insidious types of MiTM is the man-in-the-browser, also known as a banking Trojan. The most common objective is financial fraud. This form of MiTM works by means of malware that has been installed on the victim’s system. The malware is able to modify online banking transactions, so what the browser displays and what is actually sent to the bank isn’t the same. The user simply sees the intended transaction while other transactions have actually occurred in secret, without the account holder’s knowledge. This attack’s ability to bypass encryption and escape detection by antivirus programs makes it exceptionally dangerous.
3. Man-in-the-Mobile

Image Source:https://blogs.manageengine.com/desktop-mobile/
Mobile malware is also on the rise. Hackers around the world are now trying to infect mobile devices with man-in-the-mobile attacks that can capture all SMS traffic (i.e., text messages). The primary goal of this attack is to help hackers bypass two-factor authentication protection on an online account. To do this, the malware monitors the phone for any incoming mobile transaction authentication number(mTAN) and various types of transaction authentication codes sent by a financial institution. As more banks and other companies move to two-factor authentication to provide better security for their customers, more criminals will use mobile Trojans to undermine this protection. Man-in-the-mobile presents a real challenge for out-of-band-authentication systems.
4. Man-in-the App
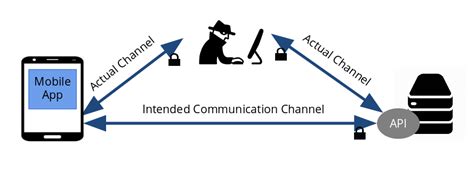
Image Source:https://softwareengineering.stackexchange.com/questions/
Not all mobile apps are as secure as they should be. Researchers found that the popular Android app Instapaper failed to do “certificate validation,” which is what apps and websites use to make sure the communication with the user is protected and can’t be hijacked. MiTA allows an attacker to insert a self-signed certificate and start communicating with the app directly. At this point, the hacker can intercept your app data, steal information, or impersonate you on the app.
5. Man-in-the-Cloud

Image Source:https://www.bitglass.com/
For any consumers who use file-sharing/storage services like Dropbox, Google Drive, Box, Microsoft OneDrive, it’s important to realize that it’s possible for cybercriminals to infiltrate them to spy on your information or infect your machine. Man-in-the-cloud exploits session management. Some cloud-based services don’t require the user to sign in each time the online account synchronizes itself between users – for example when someone uploads a shared file. Instead, they give all users a “synchronization token” which automatically verifies them each time this occurs. If hackers can steal or intercept this token, they can gain access, steal files, spread malware, and even attempt to extort users.
6. Man-in-the-IoT

Image Source:https://www.dreamstime.com/
As more “Internet of Things” and smart appliances enter our homes, they raise the potential for a new type of man-in-the-middle attack in which the hacker can take over or intercept data from our TVs, thermostats, appliances – and even our cars. These devices are equipped with at least basic operating systems and Internet or Bluetooth connectivity; however, robust cybersecurity is often not built into IoT devices as most companies seem to assume they won’t be attacked. Any networked device is a potential target of a man-in-the-middle attack. This will become a more significant issue in the future, as homes become more connected to the web.
There are ways you can defend yourself. Here are some tips that every consumer should follow to protect themselves from the various MiTM attacks…
- Never use unencrypted or free WiFi hotspots for any sensitive transactions.
- Try to always use the encrypted version of websites (i.e., make sure the URL starts with HTTPS). One way to do this is to install a browser plugin like “HTTPS Everywhere,” which seeks out HTTPS connections on any website you visit and tries to enforce it at all times.
- Make sure your home WiFi router uses WPA2 encryption, not WEP, and reset the default password to a strong 15+ character password.
- If your browser warns you that a site’s certificate has a problem, leave, don’t visit the site – ever!
- Keep the operating system, applications, and antivirus up to date on all of your devices.
- Don’t use your main home or work computer for online banking; use a dedicated laptop instead.
- Set up two-factor authentication on all of your key accounts, such as email and banking.
- Actively monitor your accounts for any changes or unusual activity.
Conclusion
The man-in-the-middle attack is a tricky one for users because most of the time victims don’t even know they’ve been hacked. The attack is silent and hard to detect unless you know precisely what you’re looking for.

